What you need to know
Cyber-crime can happen to anyone – it doesn’t matter how small your organisation is. You probably can’t stop a determined hacker, but you can make your organisation (and yourself) a harder target. It is astonishing how little care many SMEs give to this, given the risks of:
- commercially sensitive information being stolen
- theft from bank accounts
- loss or theft of others’ personal data (leading to unpleasant discussions with the ICO)
- IT not working properly
- ransomware attack, where the IT locks up completely denying access, without paying a large ransom (and even then it may not be recoverable).
![]()
Easy basics
These are things you can do that run in the background, needing little attention:
- most obviously, ensure the operating system (OS) updates itself regularly and installed software is updated, closing some vulnerabilities as they appear
- ensure all your devices (particularly laptops and mobiles – most easily stolen) are passworded and the system is encrypted when locked
- get an anti-virus system
- ensure the office Wi-Fi has a good substantial password on it, and use separate Wifi for visitors (with a different password…)
- use two factor authentication (“2FA”) where available (but preferably via a smartphone authenticator app and not via text message – it’s annoying when a dead spot stops you receiving an SMS
- do the same with home Wi-Fi (though perhaps not making it different for visitors!)
- avoid working through a public network at (e.g.) a café or pub – highly insecure
- get and use a VPN; this encrypts all of your data end-to-end, and hides your identity and location when online
- set systems and data to back themselves up frequently, so you’ve quick recovery from a successful attack; periodically test restores to check backups are working
- permit staff to use company laptops only, that can be controlled (and wiped remotely if stolen), and that don’t allow access to company confidential information except through a portal; lock down USB ports so staff cannot plug in an external hard disk or thumb drive to copy large volumes of data. The less confidential information staff have on private devices, the better
- have a plan for if it all goes wrong – including having insurance and knowing whom to call
The harder bits
Attitude
As we said in the earlier article, probably your greatest hurdle is the cavalier attitude that many – even colleagues – take to their personal cyber-security. It’s all too difficult. Get them to take it seriously, and do the same with their personal systems (at least the easy basics). If they take their own cyber-security seriously, they’ll do the same at work. If they don’t, you’ve little hope.
The big issues are passwords and social engineering attacks on you and your staff – classically “phishing”.
A word on passwords
Passwords are now a nightmare. There are so many – bank, credit card, Amazon, supermarket, trains… how to remember all of them? Many people (a) just have one, and (b) assume that the name of a favoured pet or a child or place is sufficient. This is a recipe for disaster, especially if your bank password is the same as one that is hacked.
But how to record all those different and complex and long passwords? The answer: get an app that holds them all securely under one big password, the only one you now have to remember. Or better a passphrase (not identical to the original!) such as “Maary had a li’’le lamb” – most of us can think of a slogan, motto or line of verse.
There are several such apps out there, which operate across systems, and are even at a basic level free and quite sophisticated (for example: filling out logins and passwords for you; generating passwords). They’re straightforward to download and use – encourage staff to get them for personal use too to protect their own cyber-security.
Social engineering
This is much in the news – and reporting indicates that the vast majority of successful attacks come through emails with links that recipients click on.
Staff are your first and most important line of defence – the IT team may not be able to do much once an attacker is inside. Train staff at induction to be suspicious and wary of unexpected emails. Common titles to phishing emails include “IT: Annual Asset Inventory”, “Changes to your health benefits”, “Zoom: Scheduled Meeting Error”, “Microsoft 365: Action needed: update the address”, “ Important Security Upgrade Required”. Train staff to be cautious with email addresses and domain names too: “james@my1nhouselаwyer.co.uk” (wrong) looks all too like james@myinhouselawyer.uk” (right).
And keep training the staff; successful management requires repeating messages, and there are few more important management messages than Don’t Fall For Phishing. It may save their own bank accounts too. You don’t have to manage this all yourself either; there are excellent micro learning solutions in the market to educate and test employee cyber security awareness, some allow you to conduct controlled “white hat” phishing attacks.
The good news – validation
It is now becoming affordable to subscribe to a service that checks your company firewalls, website and internet facing software for known vulnerabilities (currently over 10,000). This is like a software version of a ‘white hat hacker’ paid to look for vulnerabilities and alert you – a worthwhile investment.
Get all this right, and you’ve a much better chance that all will be well.

Written by James McLeod
Principal at My Inhouse Lawyer
One of our values (Growth) is, in many ways, all about cultivating a growth mindset. We are passionate about learning, improving and evolving. We learn from each other, use the best know-how tools in the market and constantly look for ways to simplify. Lawskool is our way of sharing with you. It isn’t intended to be legal advice, rather to enlighten you to make smart business decisions day to day with the benefit of some of our insight. We hope you enjoy the experience. There are some really good ideas and tips coming from some of the best inhouse lawyers. Easy to read and practical. If there’s something you’d like us to write about or some feedback you wish to share, feel free to drop us a note. Equally, if it’s legal advice you’re after, then just give us a call on 0207 939 3959.
Need help in this area? BOOK A CALL
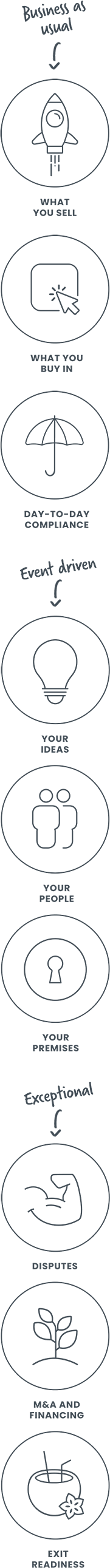
How it works
1
You
It starts with a conversation about you. What you want and the experience you’re looking for
2
Us
We design something that works for you whether it’s monthly, flex, solo, multi-team or includes legal tech
3
Together
We use Workplans to map out the work to be done and when. We are responsive and transparent
Like to know more? Book a discovery call
Freedom to choose & change
MONTHLY
A responsive inhouse experience delivered via a rolling monthly engagement that can be scaled up or down by you. Monthly Workplans capture scope, timings and budget for transparency and control
FLEX
A more reactive yet still responsive inhouse experience for legal and compliance needs as they arise. Our Workplans capture scope, timings and budget putting you in control
PROJECT
For those one-off projects such as M&A or compliance yet delivered the My Inhouse Lawyer way. We agree scope, timings and budget before each piece of work begins
Ready to get started? Book a discovery call
How we can help